By Charles Araujo. This article was originally published by Intellyx.
I remember the dreaded words ringing through the house, “Charlie, it’s time to clean your room.”
I pretended I didn’t hear, but inevitably and begrudgingly I stopped what I was doing and began the chore.
Once I was done, however, my mom explained that with my room clean we could now begin the process of transforming it from a child’s bedroom into the teenage haven I had been begging for incessantly.
Getting everything tidied up, it turned out, was the prerequisite to the transformation I so desperately wanted.
Much like “clean your room,” the term modernization has long been a dreaded word in the world of IT.
Uttering it causes involuntary shudders up the spines of IT leaders as they imagine all of the hard work, pain, and suffering to come — with almost no upside at the end of this particularly arduous road.
More importantly, the thinking has gone, while modernization is necessary, investing in it will take precious resources away from more progressive and business-critical initiatives.
So modernization efforts have been left for another day. But it is long past time for this pattern to change.
New advances in both technology and methodologies are transforming modernization from a chore into a strategic enabler — one that may now be the essential component of successful transformations in the digital era.
The problem with modernization
The trepidation surrounding modernization efforts has been well-warranted.
So-called legacy environments — the targets of modernization — are often Byzantine structures that organizations have built layer-by-layer, over the years. Each successive layer has made these systems more complex, more rigid, and almost impossible to change.
As a result, these legacy architectures have become frozen-in-time even as organizations rush to adopt modern technologies in other parts of the technology stack.
With support costs continuing to rise, organizations are recognizing that many of these legacy systems are increasingly becoming liabilities. Still, organizations have seen the pathway to modernization as daunting as they have associated it with the need to completely rewrite and rearchitect these complex and intertwined environments.
These perceived complexities, which have inhibited modernization efforts, however, are now having an even more significant effect. Organizations realize that they must connect their new, modern environments to the legacy systems responsible for core business processes to deliver the sort of end-to-end experiences that customers, partners, and employees demand.
The lack of modernization has now become a roadblock to the business transformations that are vital to an organization’s future.
This situation has left enterprises between the proverbial rock and a hard place. But perhaps modernization doesn’t need to be so difficult after all.
Three shifts that transform modernization
As the need to modernize has become a strategic imperative, both enterprises and tech companies have been exploring ways to overcome its historical challenges.
Those organizations that are finding success with their modernization efforts have discovered that the answer lies in three shifts at the intersection of new technologies and new modernization approaches.
Shift #1: from linear to iteration
First, progressive leaders have realized that they had to stop looking at modernization as a linear, one-dimensional process and, instead, see it as an iterative, modernization lifecycle.
This approach recognizes that modernization demands are themselves continually changing and that modernization is a continual effort that organizations must treat as such.
Shift #2: the move to model-driven
Second, they realized that it was a misconception that was holding them back. They believed that they could only modernize by re-platforming (attempting to transition an existing codebase to a new platform) or via Herculean “rip and replace” efforts in which they completely rewrote an application using modern code and architectures.
They have found greater success, however, with a model-driven approach in which they replicate application functionality, but do so using a combination of a refactored codebase and architectural transformation on modern platforms.
Shift #3: analysis & automation required
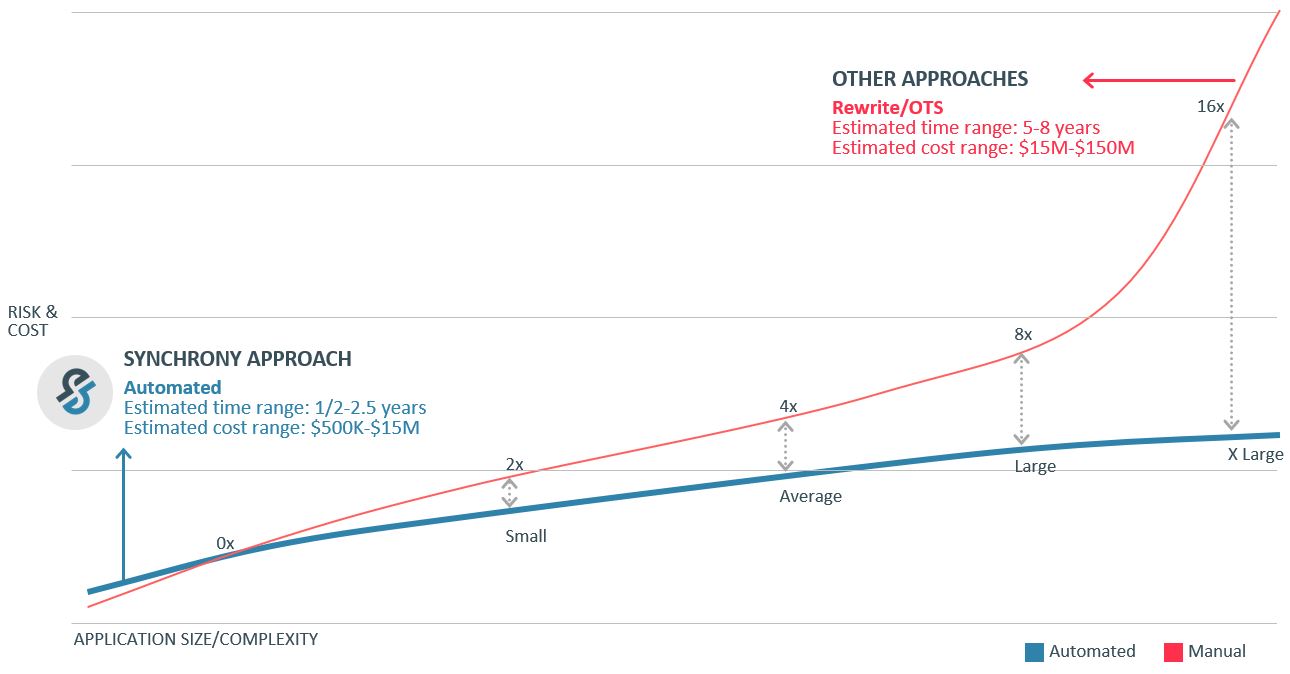
Finally, they realized that achieving this type of transformation demands codebase and workflow analysis to deconstruct and manage the modernization effort properly — and that this type of detailed analysis required automation. To achieve this third shift, organizations needed new technologies that would complete this analysis, do automated code conversion, and perform the architectural transformation in a holistic manner.
By making these three shifts, these leading organizations have been able to transform their entire approach to modernization.
The Intellyx take: from roadblock to strategic capability
For most of IT’s existence, modernization has been a nuisance. It has been something that enterprise leaders knew they should do, but which was also a burdensome chore that they would put off if at all possible.
More recently, however, the lack of modernization has become a strategic roadblock.
These rigid and challenging-to-change legacy environments are now inhibiting organizations’ ability to create the type of end-to-end experiences their customers demand.
Bringing a fresh perspective and approach to the modernization challenge, however, is enabling leading organizations to transform their modernization efforts from a roadblock to a strategic enabler.
Those organizations that can modernize their legacy environments most rapidly and effectively, in fact, are realizing a strategic advantage over their competitors that are unable to do so.
This competitive potential is why these leading organizations are turning to companies, such as Synchrony Systems, to give them the tools they need to modernize while sidestepping many of the historical challenges that kept them tied to the past.
The need to modernize legacy systems will only grow in importance as organizations drive forward with their transformational efforts. Those that get modernization right and turn it into a strategic enabler will be the ones that win in the Digital Era.
About the author