Brownfield refers to physical land requiring clean-up, upgrades, or development before leveraging the property for new purposes. Brownfield software development describes maintaining, upgrading, migrating, interacting with, or leveraging data from legacy applications.
Most of the world’s developers work on and within brownfield applications and environments. While greenfield software development gets the industry buzz, it’s the brownfield technologies with mass adoption and most usage that run companies.
Challenges in brownfield software development
Brownfield software development is not easy. The developers must keep brownfield applications up-to-date, transform critical legacy business logic to modern technologies, and architect interoperability between brownfield and greenfield applications and environments. Some key challenges with brownfield software to note are:
- Not having a thorough understanding of the legacy applications and their dependencies with other legacy platforms
- Staffing technical expertise to continue the development and maintenance of legacy applications
- Developing a strategic modernization roadmap and rapidly executing it while reducing technical risks and business disruptions
- Determining which parts of legacy applications are business-critical and must be preserved, maintained, migrated, replaced, or retired
- Managing upgrades, migrations, integrations, and modernization of legacy applications in a consistent, uniform, and repeatable manner while continuing active maintenance (no halts in development).
The inability to adequately address these issues and challenges will have a costly impact on the current and future business.
Adopt continuous modernization to help solve brownfield application development challenges
Instead of the obsolete top-down / waterfall approaches in greenfield applications, development teams have adapted leading DevOps principles such as continuous integration (CI), continuous testing, continuous monitoring, continuous security, and continuous delivery (CD) to take a more agile and iterative approach. Incorporating the continuous modernization (CM) principle to brownfield applications should be a natural extension of DevOps to enhance and fully complete the cycle of software development, maintenance, and evolution.
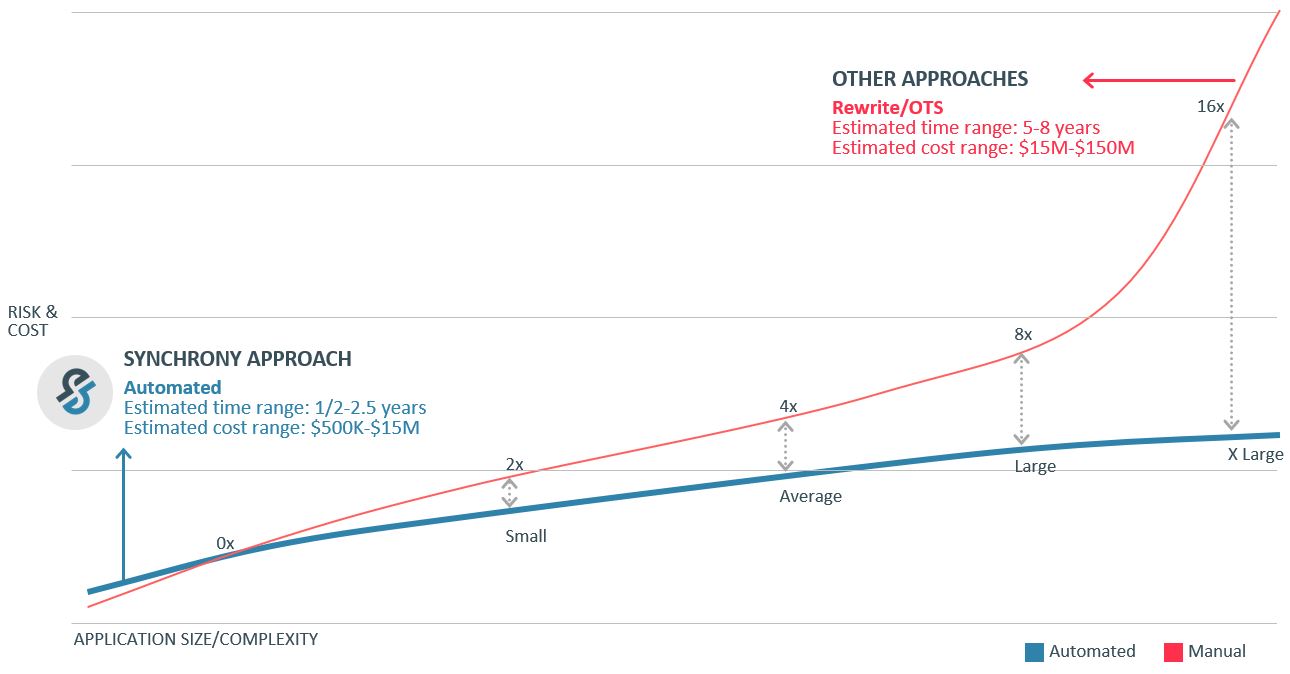
The principle of continuous modernization is to avoid the need for large, time-consuming, costly, and risky undertaking of major modernization initiatives in the brownfield software space. Executing a continuous modernization strategy requires different processes and automation tools to manage software migrations, modernizations, and upgrades while coexisting with ongoing greenfield and brownfield development projects.
One such tool is MLP, a SaaS platform that brings a uniform upgrade process, a collaborative work environment, and transparent and traceable workflows to continuous modernization. It snaps into your existing CI/CD environments and procedures to give you the ability to apply new software updates systematically and incrementally to your in-house applications, APIs, or any other software components.
Benefits of continuous modernization for brownfield software
Leveraging automated modernization workflow management tools and platforms like MLP for brownfield software upgrades, maintenance, integrations, and modernizations will benefit the business in many ways. Some of the benefits offered by continuous modernization for brownfield applications are outlined below:
- Accelerate adoption of native, cloud-first, and mobile application architecture
- Fast-track digital transformation projects to accelerate delivery of business value
- Reduce security risks associated with legacy applications
- Keep currency with a rapidly changing technology landscape
- Improve performance of brownfield applications
- Continuously eliminate creeping technical debt
- Prevent massive modernization initiatives in the future
In short, continuous modernization makes it easier to support brownfield application development by providing a systematic, uniform, and accelerated approach to executing modernization roadmaps without disrupting the day-to-day business operations.
Learn more about continuous modernization.